Architecture Overview
This document provides a high-level view of the HomeOps Server Foundation architecture. The focus is on logical components and their relationships rather than low-level implementation details.
The architecture described here represents Phase 1 of the platform: a single-node, non-segmented environment intended for learning, experimentation, and iterative hardening.
Architecture Principles (Phase 1)
The following principles guide the current architecture:
-
Single-node design
All workloads run on a single Proxmox VE host. High availability and clustering are explicitly out of scope for this phase. -
Clear separation between host and workloads
The Proxmox VE host provides the virtualization platform only. Applications and services are deployed inside virtual machines or containers. -
Bridge-based networking
All virtual workloads connect to the network via a Linux bridge on the host, enabling transparent Layer 2 connectivity. -
Simplicity over segmentation
No VLANs, network zones, or service isolation are applied in Phase 1. These are planned for later phases.
High-Level Network Topology
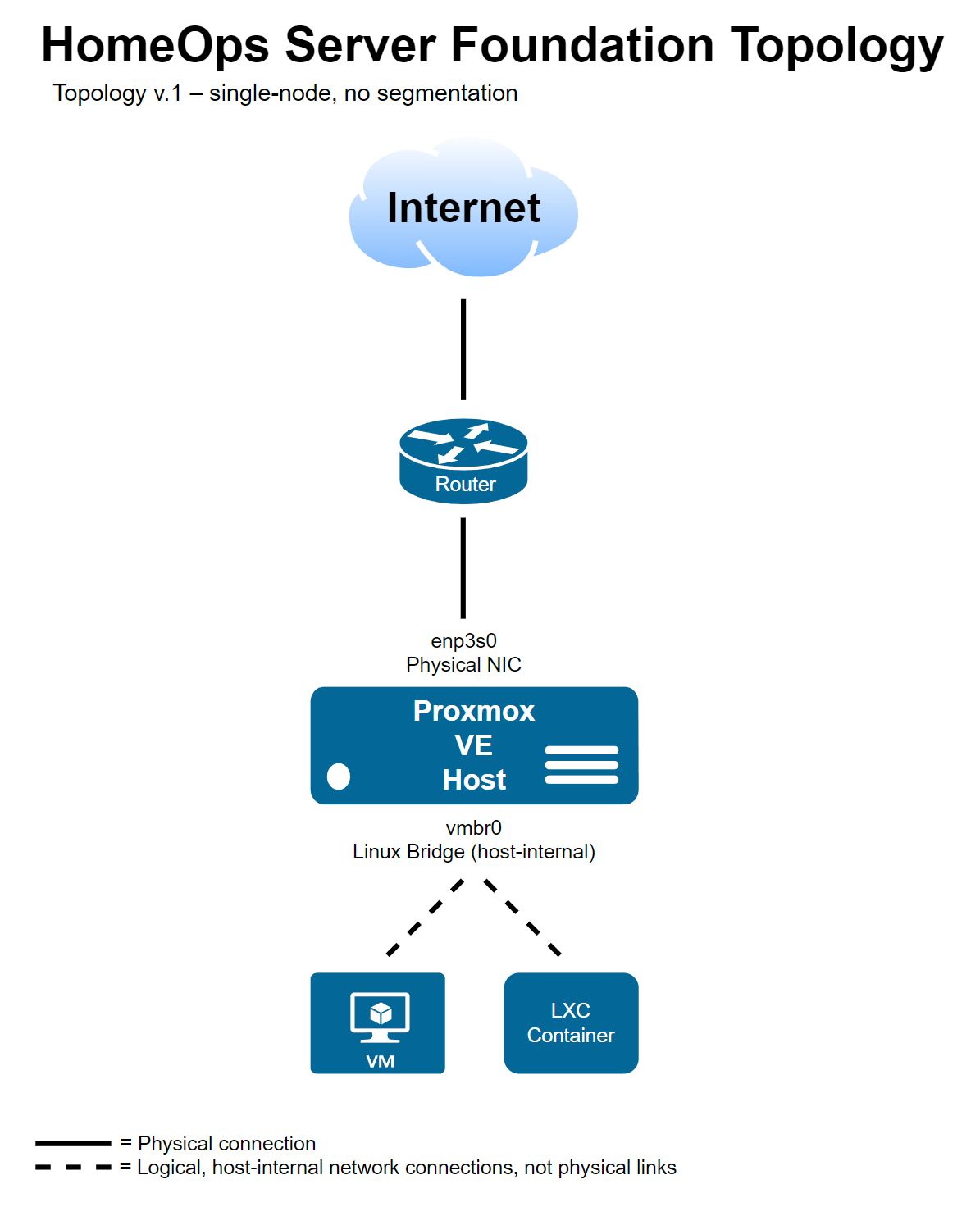
The diagram illustrates the high-level network topology of the HomeOps Server Foundation.
A single physical network interface provides external connectivity to the Proxmox VE host. The host uses a Linux bridge (vmbr0) to connect virtual machines and containers to the same Layer 2 network.
Dashed links represent logical, host-internal network connections rather than physical cabling.
Host, Storage, and Workloads
The Proxmox VE host acts as the control plane for the environment:
- The host manages hardware resources, networking, and storage.
- Virtual machines (VMs) are used for full operating system isolation.
- LXC containers are used for lightweight, host-integrated workloads.
Storage is provided locally by the host and exposed to workloads via Proxmox-managed storage backends. From an architectural perspective, storage remains host-owned and is not directly managed by individual workloads.
Update and Patch Policy (Phase 1)
The Proxmox VE host follows a semi-automated update model designed to balance security and operational stability.
Policy decisions:
- Security updates are installed automatically.
- Full distribution upgrades are not automated.
- Kernel upgrades may require manual reboot.
- Administrative review is required before major version upgrades.
Rationale:
- Reduces exposure window for known vulnerabilities.
- Avoids unattended disruptive upgrades on a hypervisor host.
- Preserves operational control over kernel and Proxmox-specific components.
Scope and Non-Goals
This document intentionally does not cover:
- IP addressing details
- Firewall rules or access policies
- Service exposure or application-level architecture
- High availability or redundancy
These topics are addressed in separate documents or in later phases of the project. Operational details such as addressing, firewall rules, and access control are intentionally excluded from public documentation and maintained only in internal project documentation.